Upcoming Events
Welcome to the gateway of empowerment and safety. In today’s fast-paced world, being alert and aware of your surroundings is not just a skill but a necessity.
In an ever-changing world, the ability to stay vigilant and aware of one’s surroundings is crucial, especially for those who travel frequently or are young adults navigating new experiences. A situational awareness course provides invaluable knowledge and skills that can make all the difference in ensuring personal safety and well-being. Whether exploring new cities, attending social events, or simply going about daily life, understanding potential risks and knowing how to respond effectively is paramount. By investing in such a course, individuals not only equip themselves with practical tools for assessing and managing various situations but also cultivate a mindset of proactive preparedness. Ultimately, mastering situational awareness empowers young adults to confidently explore the world while staying vigilant and safe.
Sign up now while spots are open!
Acceptable and responsible security companies prioritize the safety and privacy of their clients above all else. They adhere to stringent ethical standards and legal regulations, ensuring that all operations are conducted transparently and with integrity. These companies employ highly trained professionals, utilize state-of-the-art technology, and implement comprehensive security measures tailored to the specific needs of their clients. They are committed to continuous improvement through regular training and updates to their security protocols. Furthermore, they respect client confidentiality, provide clear communication, and respond promptly to any security concerns. By fostering a culture of trust and accountability, responsible security companies build long-lasting relationships with their clients and contribute to safer communities.
Traveling can be an exciting adventure, but for many, it also triggers key anxiety concerns. Effectively managing these worries is essential for enjoying your journey and making the most of your experiences. Anxiety while traveling can stem from various sources such as fear of flying, safety concerns, health issues, or the unpredictability of new environments.
To combat these feelings, thorough preparation is crucial. Start by researching your destination, understanding local customs, transportation options, and safety tips. Planning your itinerary, accommodations, and even meals ahead can alleviate stress and prevent last-minute scrambles. It’s also beneficial to pack well in advance and create a checklist to ensure you have everything you need, like medications, chargers, or specific documents.
Incorporating mindfulness and relaxation techniques can also be invaluable for managing travel anxiety. Practices such as deep breathing, meditation, or yoga can help calm your mind and reduce stress levels both before and during your trip. Keeping a travel journal can also help you process your feelings and experiences, turning anxiety into a more reflective and less overwhelming experience.
Lastly, don’t hesitate to seek support from travel companions or locals if anxiety becomes challenging. Sometimes, simply sharing your worries can lighten your mental load and enhance your travel experience. By taking these steps, you can address key anxiety concerns, transforming travel anxiety into a more manageable and controlled aspect of your journey, allowing you to focus on the joys of discovering new places.
Stay aware!
Being predictable in terms of time and location can pose several risks, especially in terms of security and personal safety. Here are some of the potential dangers:
- Vulnerability to Crime: If someone’s routines are predictable, it can make them an easy target for criminal activities such as burglary, stalking, or even physical attacks. Criminals who know when a person will not be home, or where they are likely to be at a certain time, can plan their actions with a higher chance of success.
- Loss of Privacy: Predictability can also lead to a loss of privacy. If others, including undesirable entities, can easily track someone’s movements and routines, it diminishes that person’s ability to keep aspects of their life private.
- Manipulation and Control: Individuals or entities with access to someone’s predictable patterns can manipulate circumstances to their advantage, leading to situations where the predictable individual might be coerced or controlled without their explicit realization.
- Reduced Spontaneity and Flexibility: Sticking to a predictable routine can sometimes limit a person’s spontaneity and flexibility. It can make adapting to new opportunities or changes more challenging, as deviations from the routine might cause discomfort or anxiety.
- Dependency: Over time, predictability in routines can lead to dependency, where a person might feel disoriented or unable to function properly when their routine is disrupted. This can affect mental health and well-being.

When looking for a security company, especially for services like cybersecurity or physical security, it’s important to follow best practices to ensure you’re choosing a reputable and effective provider. Here are some key steps to consider:
- Define Your Needs: Determine exactly what kind of security services you require. This could include cybersecurity, physical security (guards, patrols), access control, surveillance, risk assessments, or a combination of these.
- Research Potential Providers: Look for security companies with experience and a good reputation in your industry. Ask for recommendations from colleagues, check online reviews, and look for certifications or memberships in industry associations.
- Check Licensing and Insurance: Ensure that the company is properly licensed and insured. This helps protect you from liability in case of any incidents involving the security personnel.
- Review Experience and Track Record: Look for a company with a proven track record of providing effective security solutions. Ask for case studies or examples of their work in similar industries or situations.
- Evaluate Technology and Resources: Inquire about the technology and resources the company uses to provide security services. This could include surveillance systems, access control systems, and other security tools.
- Assess Training and Certification: Ensure that the security personnel are well-trained and certified. Ask about the company’s training programs and certifications relevant to your needs.
- Consider Customer Service: Look for a company that emphasizes good customer service. They should be responsive to your inquiries and proactive in addressing your security concerns.
- Review Contracts and Terms: Carefully review the contract terms, including pricing, services included, termination clauses, and any guarantees or warranties offered.
- Seek Multiple Bids: Get bids from multiple security companies to compare services and pricing. This can help you find the best value for your security needs.
- Get References: Ask the company for references from current or past clients. Contact these references to get their feedback on the company’s services.
Following these best practices can help you find a security company that meets your needs and provides reliable security services. Get in touch for a coffee and a consult.

The Eagle Eye Way: How a Professional Security Company Serves High Net Worth Individuals and Companies
High net worth individuals and companies need specialized security services to protect themselves and their assets. Ordinary security measures may not be enough to ensure their safety. That’s where Eagle Eye International comes in. Eagle Eye is a professional security company that provides high-level security services to its clients. In this blog post, we will discuss the Eagle Eye way, how the company operates and how its services can benefit high net worth individuals and companies.
First and foremost, what sets Eagle Eye apart from other security companies is their level of expertise. They have a team of highly skilled and professional security personnel who are experienced in dealing with various security threats. They use their expertise to provide tier-one security services, protective services, and secure logistics among others. Eagle Eye offers tailored and customized plans for their clients. They work with their clients to identify their unique needs and develop a security plan that fits those needs. This ensures that clients receive the right security measures that they need for their specific situation and environment. This tailored approach helps to ensure that clients’ security concerns are addressed effectively. Eagle Eye’s services are backed up by a robust security network that enables them to work with existing security teams. They ensure that they understand their clients’ current security environment and combine it with their expertise to provide comprehensive security solutions. This partnership leads to better coordination and communication between security teams, which ultimately improves security.
Eagle Eye is highly capable of providing global security services. They have a global reach and can work with clients anywhere in the world. Their teams are familiar with different cultures and environments, making them uniquely equipped to provide security services to high net worth individuals and companies that may have global operations or interests.
Lastly, Eagle Eye is willing to take on difficult operations. They are not a one-size-fits-all kind of security company. They thrive in challenging security situations and are always willing to go the extra mile to achieve their clients’ security objectives. They handle each situation with professionalism and efficiency, providing quality security solutions that meet their clients’ needs.
In conclusion, Eagle Eye Protective Services provides an all-rounded security solution for high net worth individuals and companies. The company offers tailored and customized plans, works with existing security teams, has global capabilities, and is willing to take on challenging operations. With Eagle Eye, high net worth individuals and companies can rest assured that they have a reliable partner in ensuring their safety and that of their assets.
“Our success is rooted in building strong and lasting relationships with our clients and providing the highest level of services possible.”


As an Ultra High Net Worth (UHNW) individual, your wealth and assets are not only a source of pride but also a prime target for potential threats. This is where the importance of protecting your family office structure comes into play.
A family office is an organization set up by UHNW individuals/managers to manage their vast wealth, investments, and other financial affairs.
It is usually a private company that provides personalized financial and investment services to the family members, including tax planning, estate planning, asset protection, and risk management.
Given the sensitive nature of the information and assets handled by a family office, it is crucial to have robust security measures in place to safeguard against threats. So how do you protect your family office structure? Here are some key steps to consider:
Develop a Comprehensive Risk Management Strategy:
A risk management strategy is essential in identifying potential threats and developing appropriate measures to mitigate or eliminate them. The first step in this process is conducting a thorough risk assessment of your family office. This involves examining the operations, processes, assets, and personnel involved to determine any vulnerabilities that could pose a threat to your office’s security.
Implement Strong Cybersecurity Measures:
In today’s digital age, cybersecurity is one of the biggest concerns for any organization, including family offices. As a UHNW individual, your family office likely handles sensitive financial and personal information that could be targeted by hackers or cybercriminals. Therefore, it is crucial to implement strong cybersecurity measures such as firewalls, encryption, multi-factor authentication, and regular security audits to protect against cyber threats.
Consider Physical Security Measures:
Physical security measures are just as important in protecting a family office structure as cybersecurity measures. This includes securing the physical premises of your family office with state-of-the-art alarm systems, surveillance cameras, access controls, and other necessary security equipment. You may also consider hiring security personnel to monitor and protect your office at all times.
Utilize Asset Protection Strategies:
Asset protection is a crucial aspect of protecting your family office structure. This involves implementing various legal and financial strategies to safeguard your assets from potential threats such as lawsuits, creditors, or other legal claims. These can include setting up trusts, using offshore accounts, or structuring ownership of assets in a way that minimizes risk.
Have a Crisis Management Plan in Place:
Despite all the precautionary measures, it is still possible for a family office to face unexpected threats or crises. Therefore, having a crisis management plan in place is essential to minimize damage and mitigate risks effectively. This plan should outline clear steps and procedures to follow in case of an emergency, including communication protocols and contingency plans.
In conclusion, protecting a family office structure requires a multi-faceted approach that includes developing a risk management strategy, implementing strong cybersecurity and physical security measures, utilizing asset protection strategies, and having a crisis management plan in place. By taking these steps, you can ensure the safety and security of your family office and its assets for generations.
The Team at Eagle Eye!
Keeping your family safe and secure is one of the most important things you can do as a responsible family member. With so many unknowns in the world, it’s crucial to take every measure possible to protect those you love. That’s where security companies come in. But with so many options available in the market, how do you know which security company to choose? It’s important to do your research beforehand, and in this article, we’ll go over some of the key factors you should consider before making a decision.
The first and foremost aspect to look for in a security company is its reputation. A good reputation is built over years of providing quality service and meeting client needs. Look for reviews and testimonials online, and ask people in your network if they have any experience with security companies. A reliable security company will readily provide references and case studies to back its claims.
Experience matters when it comes to security. You want a company that has dealt with various scenarios and knows how to handle different situations. A company that has been in the security business for a longer period of time can bring a sense of confidence and assurance to its clients. Additionally, experienced security companies are more likely to have better technology and systems in place.
Services offered: Different security companies offer various services. Some specialize in residential security, while others focus on commercial security. Some offer armed guards, while others provide unarmed personnel. Some companies also offer added services like CCTV monitoring, access control, and alarm systems. Review the services offered by the security companies you are considering, and choose the one that best matches your particular needs.
Licensing and Accreditation: A professional security company should have the appropriate licensing and accreditation in place. This will give you the confidence that the company has met regulatory requirements and follows industry standards. Check if the company you’re interested in has all the necessary licenses and certifications. You can also cross-check this information with relevant state authorities.
Cost: Finally, it’s important to consider cost when looking for a security company. Price points can vary significantly from company to company, so it’s essential to understand what you’re getting for your money. Don’t make the mistake of choosing a company solely based on the price. Instead, get multiple quotes from different security companies and compare them side-by-side. Remember, the cost should be seen in light of the level of service being offered.

So….Choosing the right security company is a critical decision. It’s important to do your research beforehand, ask the right questions, and weigh the pros and cons before making a final decision. Ultimately, the security company you choose should provide you with a sense of peace of mind, leaving you free to focus on other important things. Keep in mind, a good security company will prioritize your safety needs and work closely with you to develop a custom plan for your home or business. With these tips in mind, you can be confident in finding a security company that will protect your family and assets.
Cheers jg.
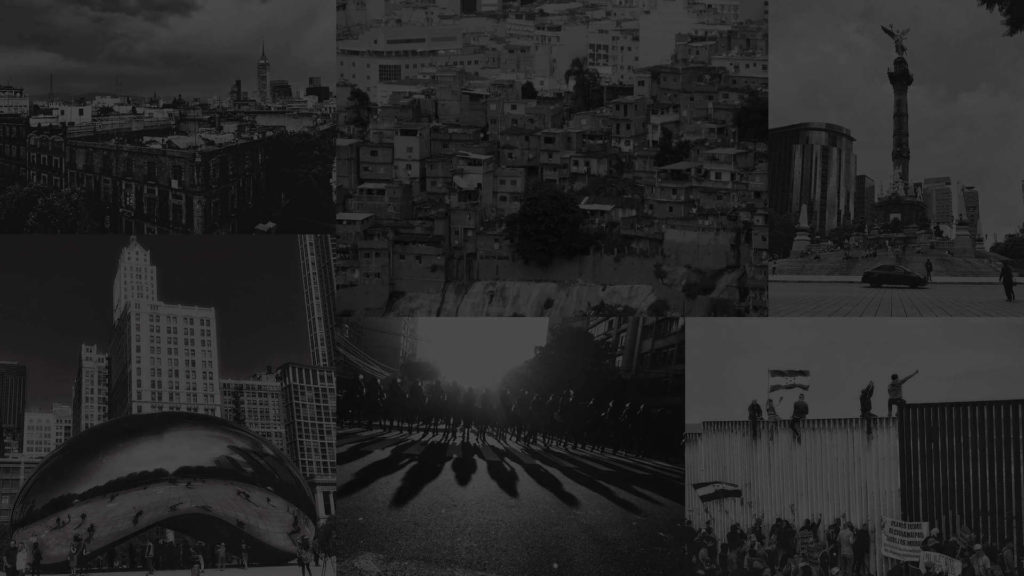
We Are a Leading Security Protective Services Company
International Protective Services for Executives and Businesses
We are a strategic level security management group comprised of highly experienced professionals that come from diverse backgrounds, ranging from industrial security, to financial services, law enforcement, military special operations, and intelligence arenas. Our executive and business security services team was formed to meet the demand for protective services in Mexico and Latin America in the 2000’s. Since then, the company has gradually moved beyond our initial niche, now secure our clients’ assets, infrastructure, and personnel throughout the United States and around the world







